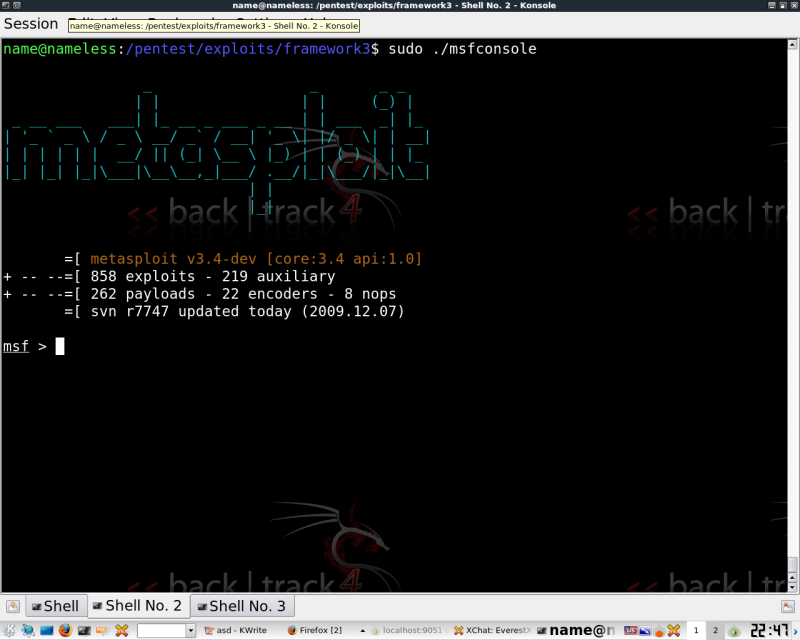
A little on the DB_autopwn feature in Framework3 BT4
If you aren't familiar with the Metasploit, you're certainly missing out on it's features.
Recently a feature called Autopwn was added. This is very familiar to the Autopwn Automation included in Fast Track.
Both Framework2, 3, and Fast Track are all included in BT4 pre by defualt.
To get the db_autopwn feature, you're going to need to update with ./msfupdate from the /pentest/exploits/framework3 dir. On most machines you should also have the svn-update.sh script.
Most of this is covered in the wonderful documentation for MSF, but hopefully this will help you get started quickly. This will help the white hats bulk test with the available exploits in meta3. For the more savvy, this will just give you a way to quickly match your larger exploit list to individual hosts.
A couple things you will need are a 1. Database, 2. a host (or hosts), 3. a port scan output, 4. Exploits
For the sake of a quick how to, I'm just going to show you how to use the db_nmap feature which automatically adds all the port scan details to the database with your host.
Then we'll breifly run through matching exploits from the db.
Then I'm going to drink beer.
*you'll need to sudo for most of this..*
Update MSF: ./msfupdate from the /pentest/exploits/framework3
1. Create your DB: db_create
Connect to your new DB: db_connect
Once you have created the DB you will no longer need to create it, you can simply use db_connect
2. Add hosts: db_add_host
Remove hosts: db_del_host
List hosts: db_hosts
3. Scan your host and add output to DB: db_nmap (whatever nmap string you want) (single host from db_hosts)
-- If anyone knows how to nmap the whole db in a single command, let me know! This part is tedious with a large db.
4. Now that your db has the nmap info, go check what exploits the ports match.
List Matched Exploits: db_autopwn -p -t
Exploit Matched Exploits db_autopwn -p -t -e
See the Meta documentation on how to connect to active sessions from, and how to use various bindshells for your exploit attacks.
Beer time.
EvX