Packet Manipulation
Snort
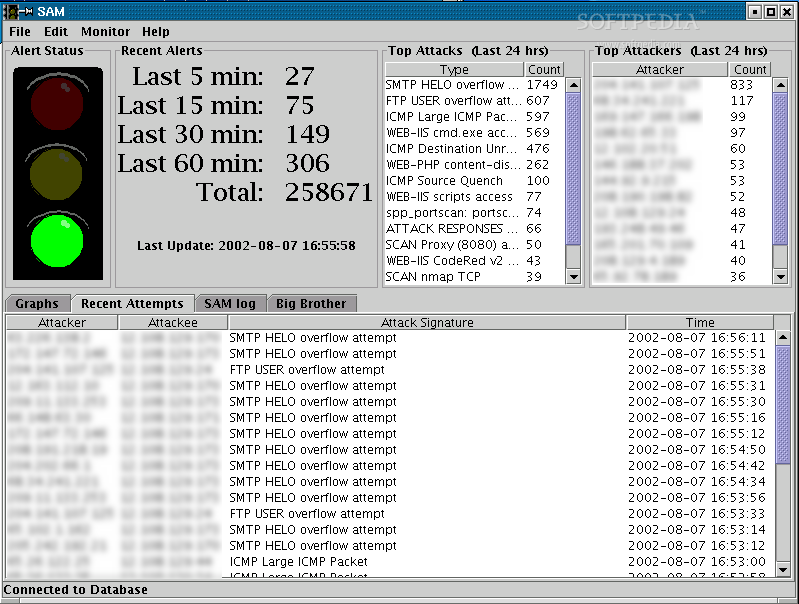
18 March, 2010 - 11:24 — greySnort is a free, open source network intrusion detection and prevention system capable of performing real-time traffic analysis and packet logging on IP networks.

Snort can perform protocol analysis and content searching/matching. It can be used to detect a variety of attacks and probes, such as buffer overflows, stealth port scans, CGI attacks, SMB probes, OS fingerprinting attempts, and much more. It uses a flexible rules language to describe traffic that it should collect or pass, as well as a detection engine that utilizes a modular plug-in architecture. Snort has a real-time alerting capability as well, incorporating alerting mechanisms for syslog, a user specified file, a UNIX socket, or WinPopup messages to Windows clients. Snort has three primary uses: a straight packet sniffer like tcpdump, a packet logger (useful for network traffic debugging, etc), or a full-blown network intrusion prevention system.
Tcptraceroute
17 March, 2010 - 15:15 — kidtcptraceroute is a traceroute implementation using TCP packets.
The more traditional traceroute( sends out either UDP or ICMP ECHO packets with a TTL of one, and increments the TTL until the destination has been reached. By printing the gateways that generate ICMP time exceeded messages along the way, it is able to determine the path packets are taking to reach the destination.
sends out either UDP or ICMP ECHO packets with a TTL of one, and increments the TTL until the destination has been reached. By printing the gateways that generate ICMP time exceeded messages along the way, it is able to determine the path packets are taking to reach the destination.
The problem is that with the widespread use of firewalls on the modern Internet, many of the packets that traceroute( sends out end up being filtered, making it impossible to completely trace the path to the destination. However, in many cases, these firewalls will permit inbound TCP packets to specific ports that hosts sitting behind the firewall are listening for connections on. By sending out TCP SYN packets instead of UDP or ICMP ECHO packets, tcptraceroute is able to bypass the most common firewall filters.
sends out end up being filtered, making it impossible to completely trace the path to the destination. However, in many cases, these firewalls will permit inbound TCP packets to specific ports that hosts sitting behind the firewall are listening for connections on. By sending out TCP SYN packets instead of UDP or ICMP ECHO packets, tcptraceroute is able to bypass the most common firewall filters.
Fping
12 March, 2010 - 01:19 — kidfping is a ping(1) like program which uses the Internet Control Message Protocol (ICMP) echo request to determine if a host is up. fping is different from ping in that you can specify any number of hosts on the command line, or specify a file containing the lists of hosts to ping. Instead of trying one host until it timeouts or replies, fping will send out a ping packet and move on to the next host in a round-robin fashion. If a host replies, it is noted and removed from the list of hosts to check. If a host does not respond within a certain time limit and/or retry limit it will be considered unreachable.
Unlike ping, fping is meant to be used in scripts and its output is easy to parse.
Unicornscan
12 March, 2010 - 01:09 — kidUnicornscan is an attempt at a User-land Distributed TCP/IP stack. It is intended to provide a researcher a superior interface for introducing a stimulus into and measuring a response from a TCP/IP enabled device or network. Although it currently has hundreds of individual features, a main set of abilities include:
* Asynchronous stateless TCP scanning with all variations of TCP Flags.
* Asynchronous stateless TCP banner grabbing
* Asynchronous protocol specific UDP Scanning (sending enough of a signature to elicit a response).
* Active and Passive remote OS, application, and component identification by analyzing responses.
* PCAP file logging and filtering
* Relational database output
* Custom module support
* Customized data-set views
Yersinia
2 March, 2010 - 02:27 — kidYersinia is a network tool designed to take advantage of some weaknesses in different network protocols. It pretends to be a solid framework for analyzing and testing the deployed networks and systems.
Tor
2 March, 2010 - 02:05 — kidTor is free software and an open network that helps you defend against a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security known as traffic analysis.
Tor protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world: it prevents somebody watching your Internet connection from learning what sites you visit, and it prevents the sites you visit from learning your physical location. Tor works with many of your existing applications, including web browsers, instant messaging clients, remote login, and other applications based on the TCP protocol.
KisMAC
24 February, 2010 - 15:42 — kidKisMAC is an open-source and free sniffer/scanner application for Mac OS X. It has an advantage over MacStumbler / iStumbler / NetStumbler in that it uses monitor mode and passive scanning.
KisMAC supports several third party PCMCIA cards: Orinoco, PrismII, Cisco Aironet, Atheros and PrismGT. USB devices with Intersil Prism2, Ralink rt2570 and rt73, and Realtek rtl8187 chipsets are in progress towards full support as well. All of the internal AirPort hardware is supported for scanning.
Firewalk
22 February, 2010 - 23:58 — kidAdvanced traceroute
Firewalk employs traceroute-like techniques to analyze IP packet responses to determine gateway ACL filters and map networks. This classic tool was rewritten from scratch in October 2002.
WebScarab
19 February, 2010 - 00:11 — kidWebScarab is a framework for analysing applications that communicate using the HTTP and HTTPS protocols. It is written in Java, and is thus portable to many platforms. WebScarab has several modes of operation, implemented by a number of plugins. In its most common usage, WebScarab operates as an intercepting proxy, allowing the operator to review and modify requests created by the browser before they are sent to the server, and to review and modify responses returned from the server before they are received by the browser. WebScarab is able to intercept both HTTP and HTTPS communication. The operator can also review the conversations (requests and responses) that have passed through WebScarab.
P0f
17 February, 2010 - 20:03 — kidP0f v2 is a versatile passive OS fingerprinting tool. P0f can identify the operating system on:
- machines that connect to your box (SYN mode),
- machines you connect to (SYN+ACK mode),
- machine you cannot connect to (RST+ mode),
- machines whose communications you can observe.
P0f can also do many other tricks, and can detect or measure the following:
- firewall presence, NAT use (useful for policy enforcement),
- existence of a load balancer setup,
- the distance to the remote system and its uptime,
- other guy's network hookup (DSL, OC3, avian carriers) and his ISP.
